Jersey’s bus operator LibertyBus suffered a weeks-long security breach of their website recently, during which attackers redirected bus riders to a fake checkout page and stole their login credentials. They say their website was compromised from about 29th April until 15th May.
If you used the LibertyBus website recently to top up your AvanchiCard, you must immediately change your password. If you use that same password at other websites, change it everywhere. Attackers will test your password on popular sites, so by using different passwords everywhere you eliminate that risk. Do this even for unimportant sites because each site collects different data points, such as a postcode or phone number, and attackers can build a profile good enough to impersonate you or to reset your password elsewhere.
The Radio Interview
LibertyBus’s Managing Director Kevin Hart was interviewed by James Hand on BBC Radio Jersey Friday 17th May. Much of this blog post is based on facts reported in that interview, so please have a listen at the BBC iPlayer, or try the embedded audio player below.
LibertyBus say their website is now safe to use, and that “…all the security on the hosting company we use has been upped…” (@3:15) and “…everything is as tight as a drum now…” (@8:28).
Tight as a drum? I am picturing Keith Moon’s kit just after the dynamite trick. I also note that LibertyBus do not appear to have security monitoring in place. They did not detect this breach until after their payment processor contacted them to enquire why all payments had ceased (@2:25)! As of today’s date, two more weeks have passed since the interview and the security of their website and server still rates extremely poorly. This is cause for concern.
To their credit, LibertyBus say they are a social enterprise which they describe as “…a business that trades to tackle social problems, improve communities, people’s life chances, or the environment - a way of doing business that puts people and the planet first.” I like LibertyBus and frequently use their buses to get around the island. The drivers and staff at Liberation Station are first rate. Let’s give the company a break for now, and learn how to avoid similar incidents going forward.
As an aside, digital is only part of LibertyBus’s operation. I have no clue how to run a transportation service and I do not expect them to know everything about securing a web server. I think many of the flaws detailed below are the responsibility of their hosting company to correct. Technical competence of web hosts varies, so choose wisely and always test marketing claims with the tools described below.
The Breach Announcement
Let’s begin with something simple, the announcement of the data breach. The address shared on social media was http://m.libertybus.je/index.php?content=News&item=459. That isn’t a secure link and no secure version of that page is available. If you are announcing a data breach or a website hack…put it on a secure page!
Testing the Web Server
One of the simplest ways to test a website’s security is to use Sucuri’s free SiteCheck service, which lists common problems. Testing libertybus.je today reveals numerous easily resolved issues, such as very old versions of software packages.

At time of posting, the software responding to user requests for web pages is Apache version 2.2.15, released way back in 2010. That is ancient. It is best practice to hide the version number of your web server but it is publicly visible for their website. The version number can be hidden from public view with ServerTokens Prod in the main Apache configuration file.
Another outdated piece of software their website runs is PHP version 5.3.3, also released back in 2010. PHP is a server scripting language used to build the pages that the server returns to users browsing the site. The version number for this should also be hidden from public view with Header unset X-Powered-By in the main Apache configuration file.
Both these software packages have received thousands of updates since 2010, including many security patches, and it is unclear why anyone would still be using such old versions. I am impressed by the fact that this website still works at all.
The above can be remedied by updating Apache and PHP to modern versions, or by switching to a better web hosting company.
Testing the Encrypted Connection
The security of the encrypted connection to the LibertyBus website can be tested with SSL Labs’s server test. Their home page leaves end users vulnerable to attack because it supports obsolete connection protocols. They have numerous hard-coded insecure http://... links to page assets, which modern browsers will not load. This is the work of someone very inexperienced.
Checking their dedicated online shop page at shop.libertybus.je also reveals a poor score with many essential modern features missing. At time of posting that checkout page was hosted on a completely different server in Bulgaria.
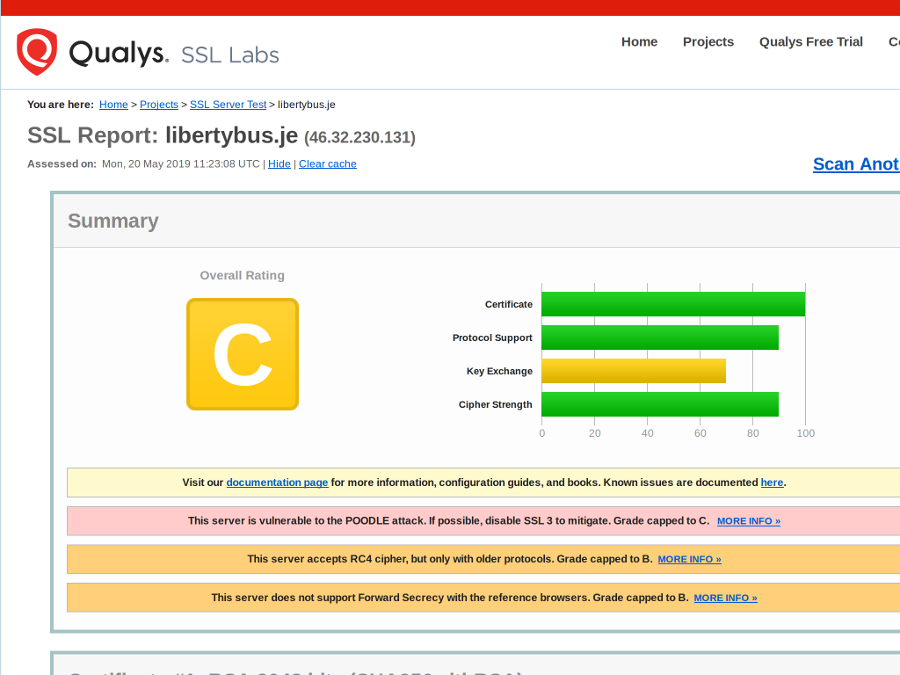
The above can be remedied by using a tool such as the Mozilla SSL Configuration Generator to produce a secure server configuration.
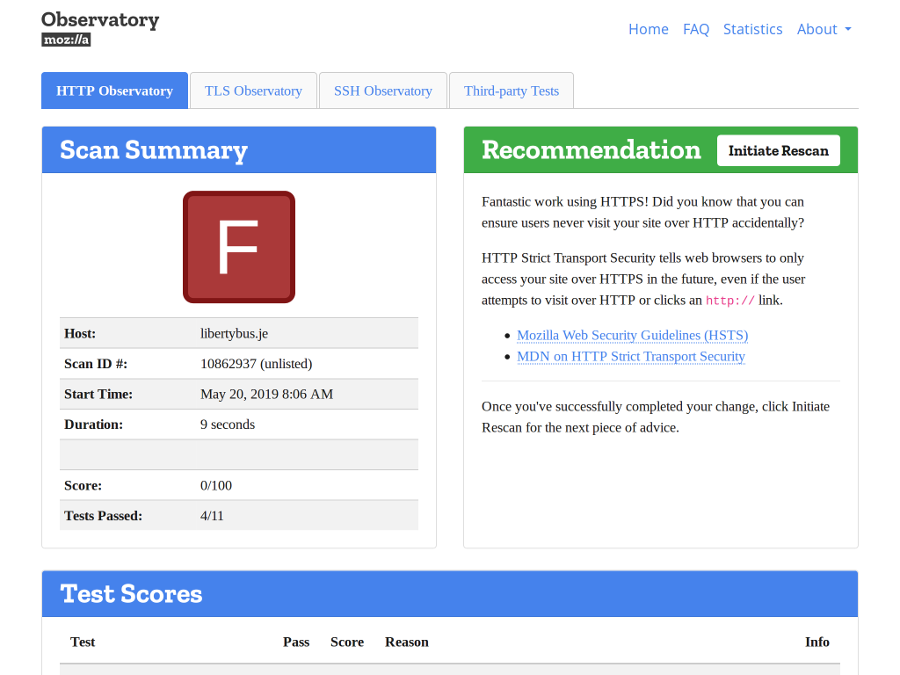
Testing the Website
Another excellent third-party scanning tool is the Mozilla Observatory, which reveals some extremely poor results. Operators of web servers may include various security instructions (called ‘headers’) along with the pages end users see. These instructions are handled automatically by web browsers and they can greatly increase security for websites and their users. Sadly LibertyBus are not using any of them, scoring zero out of 100 points in this test.
These security instructions are critical for locking down a website and controlling what third-party content may be safely displayed, and can mitigate other vulnerabilities not yet discovered, even if your website is hacked. Security headers are extremely important and if your web host does not support them, you are using the wrong web host.
The Company’s Response
After a breach, companies and news reports frequently focus on whether payment card data was stolen. While this is a minor concern for users, liability is very limited and let’s be honest, it is really your bank’s problem to resolve. Check your statements each month, look for anything unusual, and if you spot anything report it to your bank. In nearly every instance they will refund the entire amount and issue you a new card. This is due to consumer protection laws which limit your liability.
What is far more important is your personal info. Changing bank cards is easy. Changing your address, date of birth, or email address…not so simple. Never mind the bank cards, that is a distraction and not a very important point to focus on. If you were affected by this breach attackers can see any personal info listed in your account, and can test reusing your email address at other popular services to access data about you there as well. This is the real threat.
Conclusion
If you are a bus rider and need to top up your AvanchiCard, the safest way to do that is in person at Liberation Station. From the tests above it is clear that there is a lot of work to do before the LibertyBus website meets basic security standards.
If you are a business owner wondering whether your website is secure, try running the tools highlighted above to learn if your site and web hosting are competently managed. Ask questions of your web host, they should be able to explain their security and should have documentation showing you how to implement better security practices (some even do this for you automatically and by default). If you process personal data and they cannot demonstrate robust security, and independently verify this with third-party tools, find web hosting elsewhere. Try the Digital Jersey member directory as a good starting point.
As always, if you represent a Jersey Registered Charity and have questions about the security of your website, please get in touch. I can assist you at no charge, or refer you to a competent local expert.